About 34,539 results found.
(Query 0.01800 seconds)
- All
- Images

Email Heaven?! PGP Emails to Proton WITHOUT using Proton
privacyy3tsy4mge4qmg4nsid2vnhl7szzupphhkfsxvayx5tl2ztbqd.onion

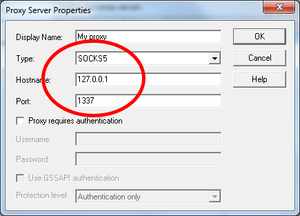
V2RayN folder showing extracted files
gpp6nwvsps43b3mfacsh433uroo6uyjvvpr6tgj4jh4n5ngxt7rqbvid.onion

NaiveProxy files extracted from the zip file
gpp6nwvsps43b3mfacsh433uroo6uyjvvpr6tgj4jh4n5ngxt7rqbvid.onion
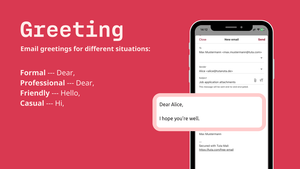
Wie man eine E-Mail beginnt: E-Mail-Grüße für verschiedene Situationen. Förmlich und professionell: Sehr geehrt. Freundlich: Hallo. Lässig: Hallo.
tutacomm6oqwlbbpd246mljjxpupuxxqj2jg5mfdyegeaetdauigslad.onion
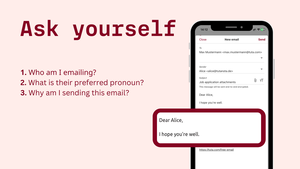
Wie man eine E-Mail beginnt: Bevor Sie beginnen, fragen Sie sich: An wen schreibe ich? Welches ist das bevorzugte Pronomen? Warum sende ich diese E-Mail?
tutacomm6oqwlbbpd246mljjxpupuxxqj2jg5mfdyegeaetdauigslad.onion
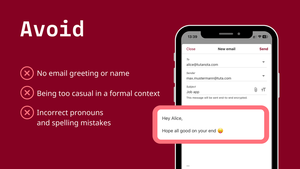
Wie man eine E-Mail beginnt: Vermeiden Sie keine E-Mail-Begrüßung oder Namensnennung. Zu leger in einem förmlichen Kontext sein. Falsche Pronomen und Rechtschreibfehler.
tutacomm6oqwlbbpd246mljjxpupuxxqj2jg5mfdyegeaetdauigslad.onion
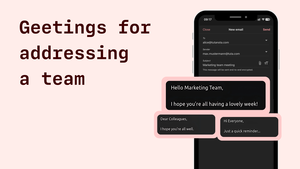
Wenn Sie eine E-Mail an eine Gruppe oder ein Team senden möchten, können Sie auch
tutacomm6oqwlbbpd246mljjxpupuxxqj2jg5mfdyegeaetdauigslad.onion
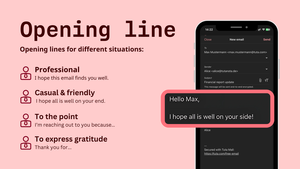
Wie man eine E-Mail beginnt: Eröffnungszeilen für verschiedene Situationen. Professionell: Ich hoffe, diese E-Mail erreicht Sie gut.
tutacomm6oqwlbbpd246mljjxpupuxxqj2jg5mfdyegeaetdauigslad.onion
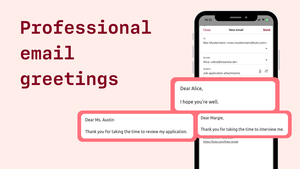
Wie man eine E-Mail professionell beginnt.
tutacomm6oqwlbbpd246mljjxpupuxxqj2jg5mfdyegeaetdauigslad.onion
Bevor Sie mit dem Schreiben der E-Mail beginnen: Fragen Sie sich, an wen ich die E-Mail schreibe? Welches ist das bevorzugte Pronomen? Und warum sende ich diese E-Mail.
tutacomm6oqwlbbpd246mljjxpupuxxqj2jg5mfdyegeaetdauigslad.onion
Die Eröffnungszeile: Ich hoffe, Ihre Woche verläuft gut / ich hoffe, es geht Ihnen gut.
tutacomm6oqwlbbpd246mljjxpupuxxqj2jg5mfdyegeaetdauigslad.onion

Was man beim Verfassen einer E-Mail vermeiden sollte: Ich weiß, dass Sie viel zu tun haben, aber könnten Sie mir bitte einen Gefallen tun? An alle, die es betrifft. Darf ich mich vorstellen?
tutacomm6oqwlbbpd246mljjxpupuxxqj2jg5mfdyegeaetdauigslad.onion
Unlike the telephone and post which have had their day and faded out of fashion, email has no expiry date! Sending emails will remain the constant form of online communication.
tutacomm6oqwlbbpd246mljjxpupuxxqj2jg5mfdyegeaetdauigslad.onion
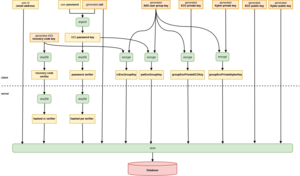
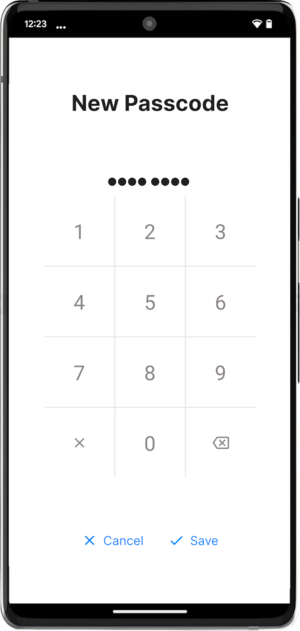
Eine Visualisierung des Umgangs mit Passwörtern und Verschlüsselungscodes.
tutacomm6oqwlbbpd246mljjxpupuxxqj2jg5mfdyegeaetdauigslad.onion
Word-of-mouth lets Tuta grow - more than 80% of our users recommend our private email and calendar service.
tutacomm6oqwlbbpd246mljjxpupuxxqj2jg5mfdyegeaetdauigslad.onion
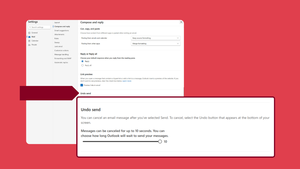
Wie Sie das Rückgängig Machens vom Senden in Outlook einrichten.
tutacomm6oqwlbbpd246mljjxpupuxxqj2jg5mfdyegeaetdauigslad.onion
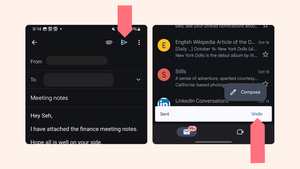
Wie Sie eine E-Mail bei Gmail auf Android zurückrufen.
tutacomm6oqwlbbpd246mljjxpupuxxqj2jg5mfdyegeaetdauigslad.onion

Facts about Bitcoin Mixing and Bitcoin Blending
coino2q64k4fg3lkjsnhjeydzwykw22a56u5nf2rdfzkjuy3jbwvypqd.onion

Cryptocurrency and the World of Bitcoin Mixer
coino2q64k4fg3lkjsnhjeydzwykw22a56u5nf2rdfzkjuy3jbwvypqd.onion

Gmail knows what you clicked last summer.
tutacomm6oqwlbbpd246mljjxpupuxxqj2jg5mfdyegeaetdauigslad.onion